Many companies depend on payment processing companies to manage their online payments. However, completely relying on a third party can lead businesses to underestimate their payment gateway security risks and requirements, opening them up to data breaches and cybercrime. This issue only becomes magnified when companies undergo changes like expanding operations or migrating to a subscription billing model.
A study by PWC, Global Economic Crime and Fraud Survey 2022, found that 52% of companies with global annual revenues exceeding $10 billion experienced fraud in the past 24 months, with 18% losing over $50 million in their most disruptive incident. Among smaller companies earning less than $100 million annually, 38% experienced fraud; of those affected, 22% faced a total impact of over $1 million.
Therefore, online payment security must be a top priority to safeguard your business. Keep reading to discover five payment gateway security features every business needs to process transactions securely.
What is a payment gateway?
A payment gateway is an e-commerce merchant service that collects customers’ payment information to authorize a transaction, ensuring that the payment is legitimate. Payment gateways read, encrypt, and transmit data between the merchant’s website, the customer’s financial institution, and the merchant’s financial institution.
Further reading: Online payment gateways bring these 5 benefits
Why is payment gateway security important?
Payment gateway security is vital to guarding your customers’ personal data and protecting your company. Security breaches, fraud, and compliance violations are all costly mistakes that not only sacrifice your hard-earned revenue but jeopardize your brand’s reputation.
Under the European Union General Data Protection Regulation (GDPR), breach or theft of cardholder data can result in penalties of up to €20 million or 4% of annual global turnover, whichever is greater.
Additionally, payment providers can fine companies who breach the Payment Card Industry Data Security Standard (PCI DSS) $5,000–$100,000 per month for non-compliance.
Therefore, as more customers embrace e-commerce for their purchasing needs, companies must be ready to provide a secure shopping experience.
Top 5 payment gateway security features
Continuous learning is foundational to creating a culture of data security, so it’s critical that your team remain updated on the latest safety strategies and regularly evaluate whether it’s time for an upgrade. Below you’ll find five payment gateway security features that are necessary in today’s business climate.
1. PCI DSS Compliance
Any company that processes credit or debit card purchases must comply with the international rules and regulations stated in the Payment Card Industry Data Security Standard (PCI DSS). The main role of the PCI DSS is to provide businesses with a standardized approach to rigorous, secure transaction processes while retaining a smooth customer experience.
Maintaining PCI compliance is essential to avoiding penalties and improves your reputation with payment brands, builds customer trust, and bolsters your systems to prevent data breaches and credit card fraud. The PCI DSS has 12 key requirements, further broken down into 78 base requirements and 400 test procedures. The 12 key requirements are outlined in the image below:
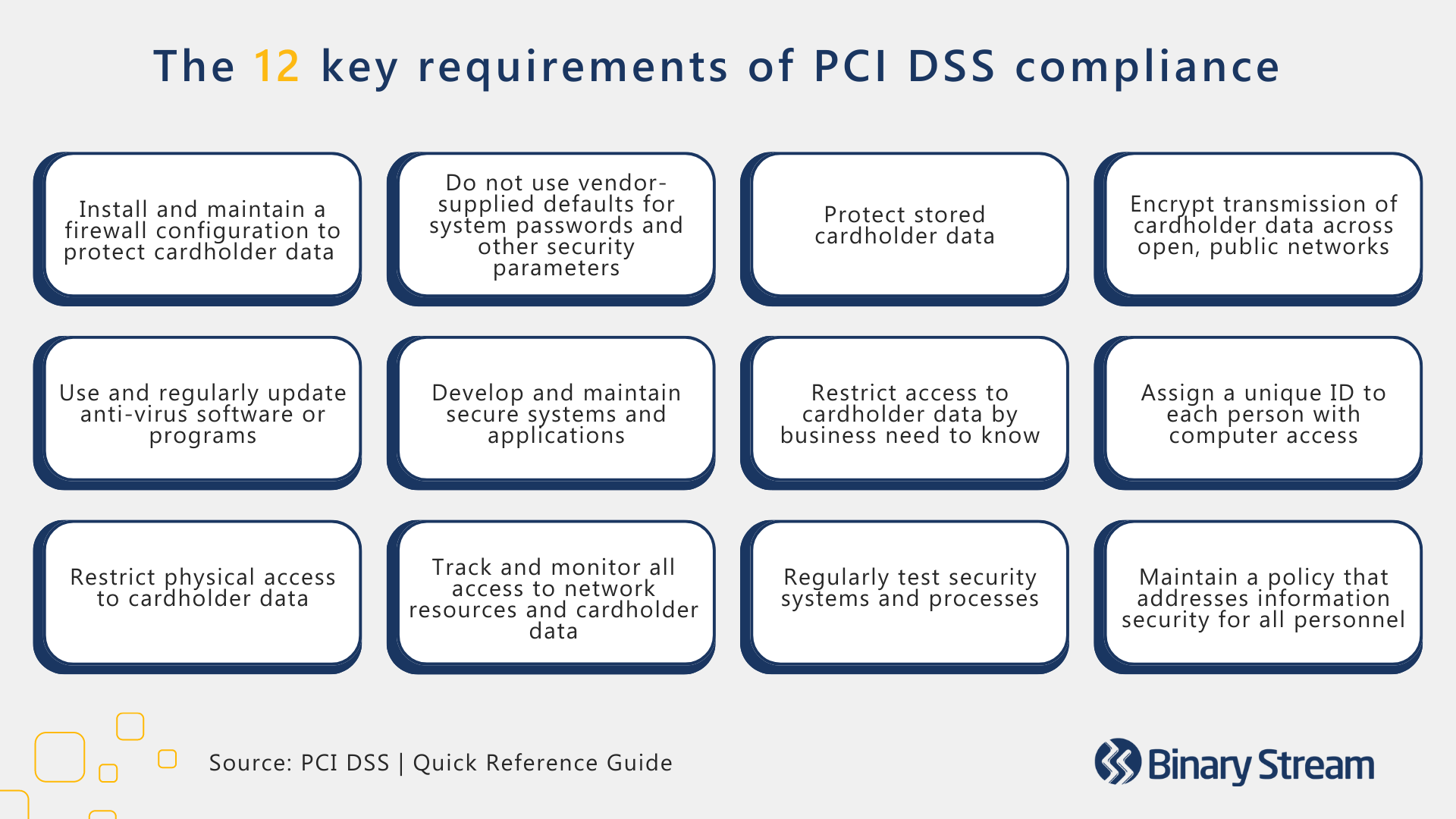
Companies must adhere to different compliance levels based on their size. The PCI classifies businesses on a four-level scale by the number of transactions they process per year:
- Level 1: >6 million card transactions annually.
- Level 2: 1–6 million card transactions annually.
- Level 3: 20,000–1 million card transactions annually.
- Level 4: <20,000 card transactions annually.
All legitimate processing providers are required to offer PCI-compliant services; however, it’s still worth investigating the PCI DSS as your business will be on the line for any non-compliance. When determining which payment processor to invest in, make sure it can manage credit card processing, transaction history, and credit card data management while complying with the PCI DSS.
2. SSL and TLS protocols
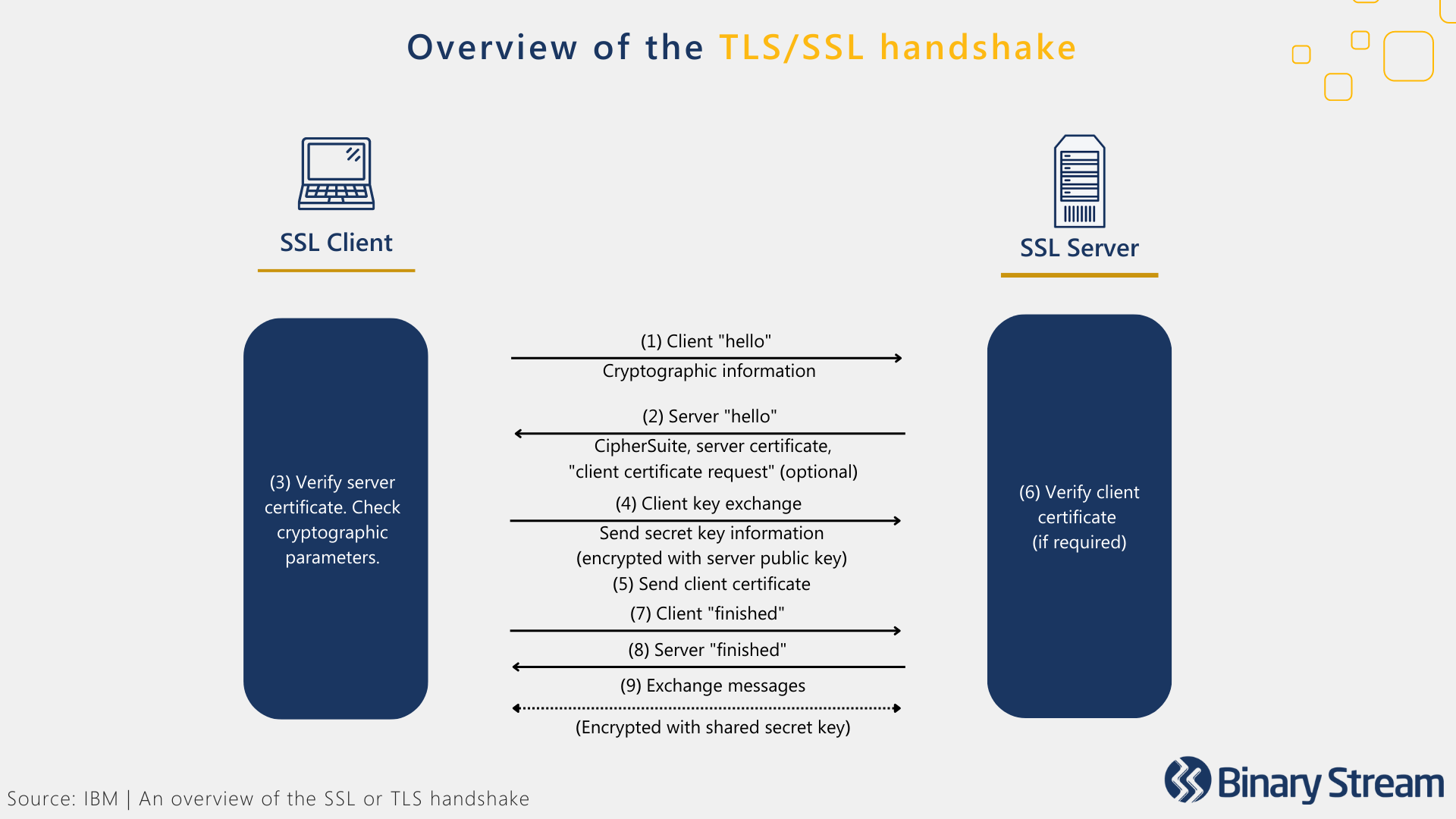
Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocols encrypt the online connection between the browser and the server, creating end-to-end protection for sensitive information. These security measures ensure the secure transmission of customer data collected by a payment gateway.
Here’s an overview of how the encryption process, nicknamed the “TLS/SSL handshake,” works:
- Each TLS/SSL certificate involves a public key and a private key.
- When a customer visits the website, the customer’s server and the web browser communicate to determine if there’s a secure TLS/SSL encrypted connection.
- When the web browser directs to the website, the website server shares its TLS/SSL certificate and public key with the customer to establish a secure connection, generating a unique session key.
- The browser confirms that it recognizes the issuer of the TLS/SSL certificate (Certificate Authority) and that the certificate is not expired, revoked, or untrustworthy.
- The browser sends over the session key, and the server uses its private key to decrypt the session key.
- The server then sends back an encrypted acknowledgment using the session key to start the encrypted session.
- The server and browser can now encrypt all transmitted data with the session key, creating a secure session that fortifies all shared data’s privacy, integrity, and security.
If you’ve ever visited a website where the URL begins with HTTPS or has a padlock symbol next to it, then you’ve encountered TLS/SSL encryption. These hallmarks signify that the website is TLS/SSL certified and that your customers can trust your company with their payment information.
3. 3D Secure
3D Secure (3-domain structure) or payer authentication, is a security feature that addresses issues of fraud in online debit or credit card transactions. Customers are required to complete an extra step of verification with their card issuer at checkout, engaging all three domains of payer authentication:
- The merchant/acquirer domain
- The issuer domain
- The interoperability domain
The most recent iteration, 3D Secure 2, allows for different methods of verification other than a password, including:
- 2FA (2 factor authentication): Using two different authentication factors, such as a username and password combination and a phone.
- Biometric identification: fingerprint, face, or voice recognition.
- Risk-based authentication: a flexible approach to authentication, requiring different protocols based on the customer’s risk profile.
4. Tokenization
Tokenization secures customer payment details by replacing sensitive data with a string of randomly generated numbers, referred to as a ‘token.’ The PCI DSS promotes the adoption of payment tokenization with good reason.
Tokens provide one-to-one replacements for primary account numbers kept outside the merchant’s server. The merchant does not need to be responsible for storing sensitive information, protecting the merchant and customer against fraudulent activity.
This extra layer of protection renders confidential information meaningless and useless in a breach. If a hacker were to gain access to the tokens, their efforts would be wasted because they would have no way to decrypt them.

5. Address Verification Service
The address verification service (AVS) is another commonly used method to prevent credit card fraud. After a customer enters their billing address, AVS will check if it matches the one on file with the credit card provider. If it’s a match, then the transaction will be approved.
AVS can be an effective protocol for minimizing chargebacks. Verifying details about the cardholder provided during the purchasing process can help flag suspicious transactions and protect the company before fraud occurs.
Further reading: The ultimate checklist for the best recurring billing payment gateways

